[ad_1]

Remain vigilant against hostile campaigns
– Jonathan Zhang, CEO at Whois XML API
Walnut, Calif. – Mar. 15, 2022
24 February 2022 is one of the most significant days in recent history as it signaled the culmination of the enmity between Russia and Ukraine. Like any armed conflict, it had spillovers. Several nations have declared economic war against Russia. Civilians in both countries are suffering, and those in other countries are bound to feel some impact as well.
Being at the forefront of domain and Domain Name System (DNS) intelligence, we also saw another kind of spillover — the digital sort. More than 5,000 unique domains and subdomains were added to the DNS less than two weeks after the conflict started. Only time can tell whether these cyber resources will spell heightened cybercriminal activities in direct or indirect connection to the conflict.
Still, organizations must remain vigilant against malicious campaigns related to the ongoing situation, regardless of where they may come from. We analyzed relevant domains and subdomains to provide actionable domain intelligence relevant to this call. Among our findings are:
- More than 3,900 newly registered domains (NRDs) containing relevant text strings, such as combinations of “ukraine,” “russia,” “donation,” “donate,” and “support,” were created between 24 February and 3 March 2022.
- Over 2,100 subdomains containing the same text strings made it into the DNS within the same period.
- Screenshot analyses of donation- and support-related domains and subdomains revealed different types of hosted content.
- More than 1,000 of the digital properties actively resolved to 670 unique IP addresses.
You may download the complete research materials from our website. We also provide an overview of the findings below:
The Anatomy of Domains and Subdomains Following the Russia-Ukraine Conflict
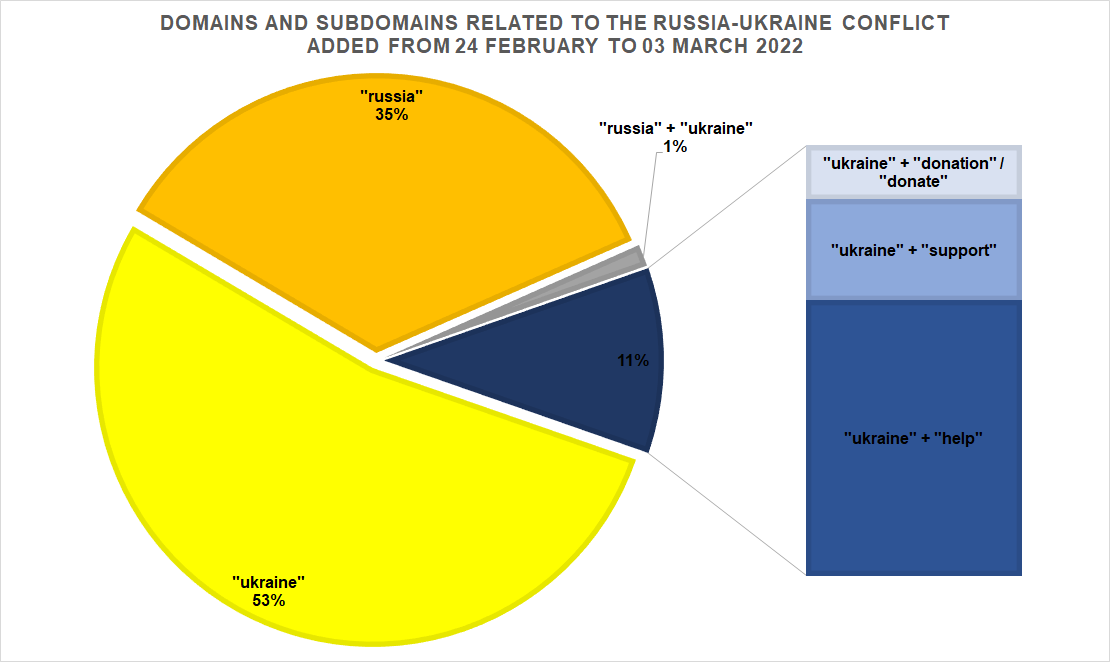
To get a sense of how the ongoing tension has affected domain registration, we used the search strings “ukraine,” “russia,” and “russia + ukraine.” We also searched for web properties using “ukraine” alongside targeted text strings, such as “donation” “donate” “help” and “support.” You can see the distribution of the results in the chart below.
About 65 percent of the cyber resources contain the “ukraine,” around 747 of which were used alongside “donate,” “donation,” “help,” and “support.” We also tried using the exact search strings alongside “russia,” but that did not yield significant results.
Where Do Calls for Help Come From?
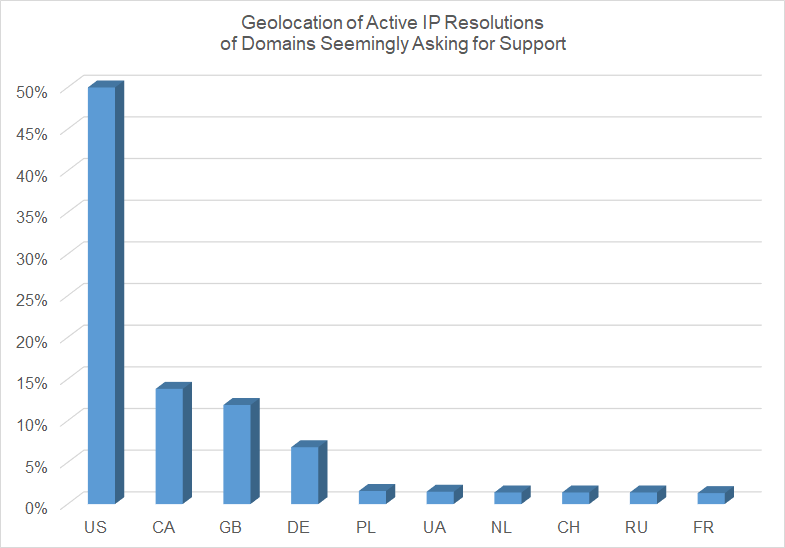
We focused our subsequent analysis on the 747 digital properties seemingly asking for donation, help, and support. As of this writing, 87 percent of these domains actively resolved to 670 unique IP addresses, totaling 1,143 resolutions. Where do these IP resolutions come from?
Our analysis pointed to the U.S. as the origin of half of the active resolutions. Other North Atlantic Treaty Organization (NATO) countries were also on the top 10 geolocations — Canada, the U.K., Germany, Poland, France, and the Netherlands. IP resolutions also originated from non-NATO members, including Ukraine, Russia, and China.
What Content Do the Domains Host?
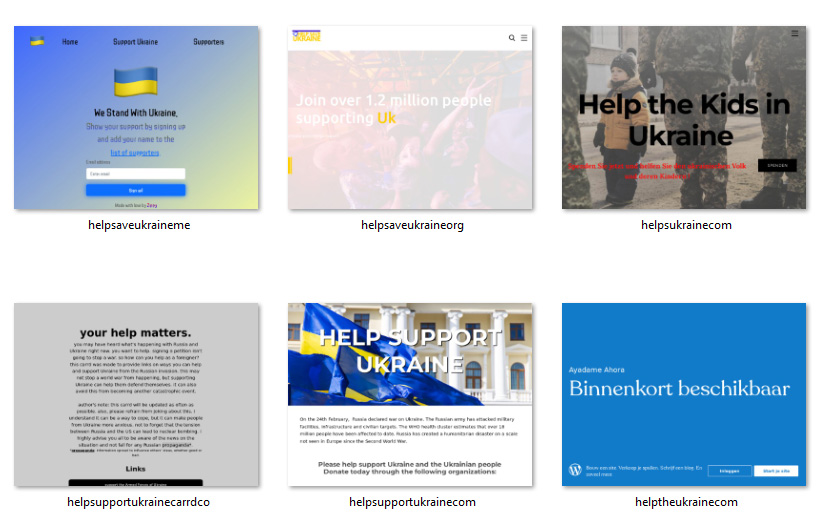
Hundreds of domains subjected to further analysis hosted content asking for donations. Some examples are shown below.
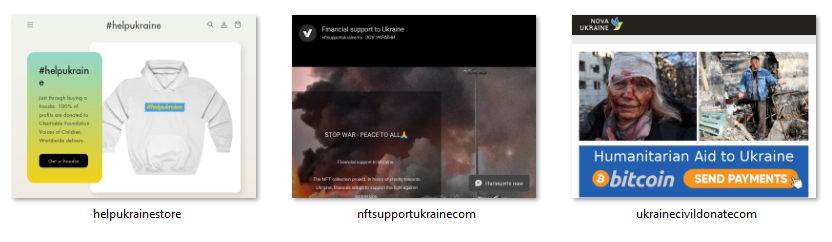
Some content immediately provided information about specific ways people can help, such as buying merchandise or donating Bitcoin or nonfungible tokens (NFTs).
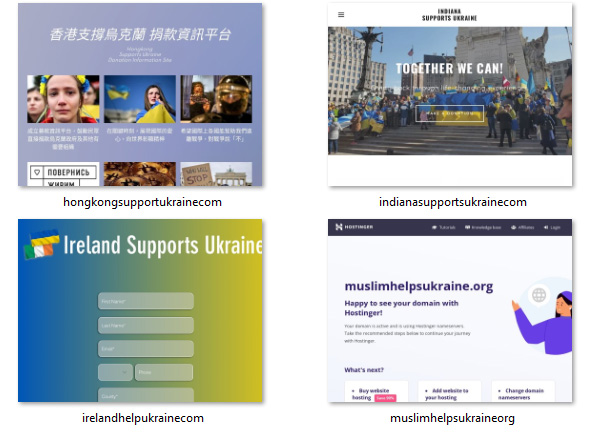
Other domains hosted content targeting specific countries or groups of people (see the screenshots below).
There were also domains hosting news-related content.
Malicious Properties Detected
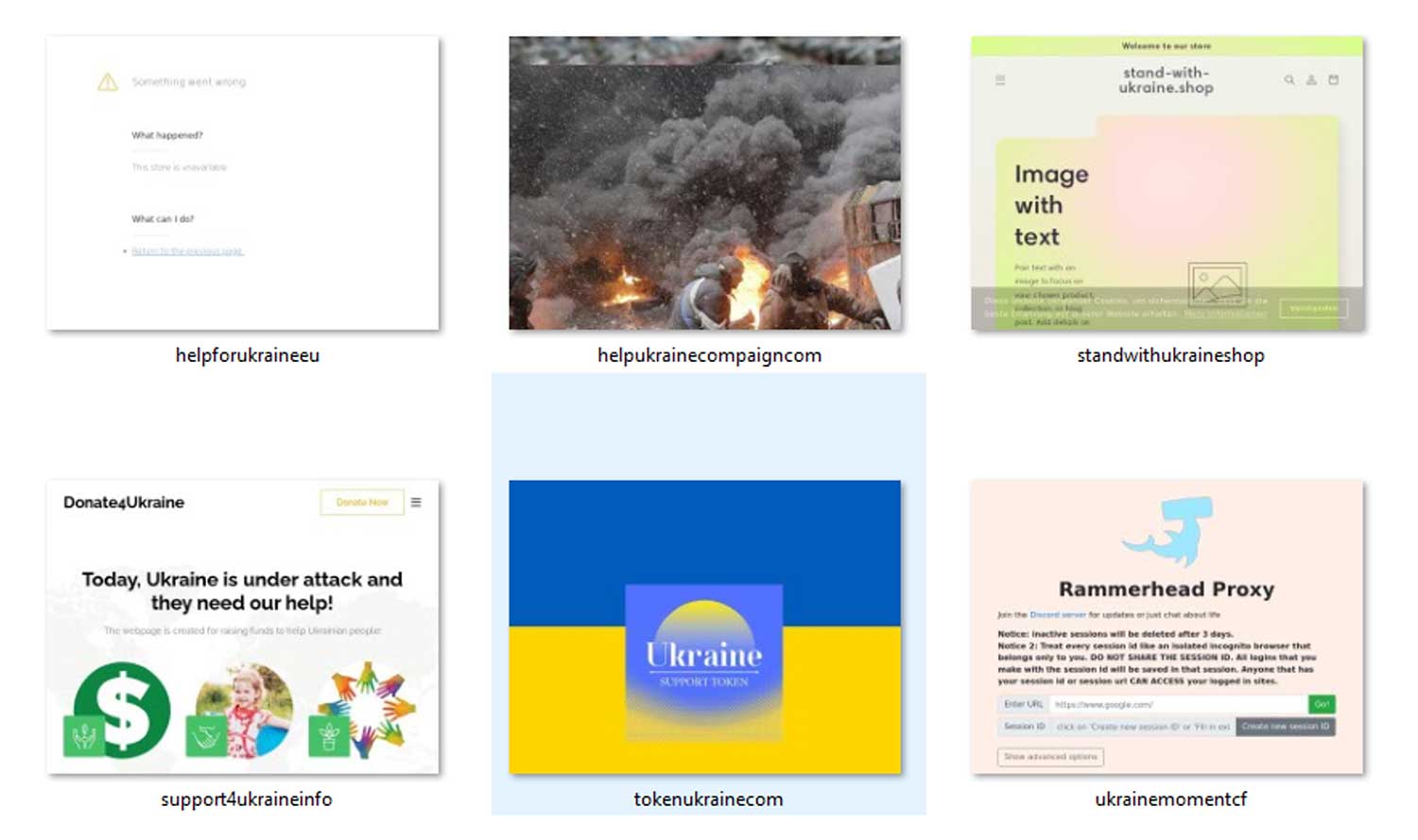
Several domains in the study have already been flagged as malicious, some seemingly in support of Ukraine, alluding to fundraising campaigns. Here are some examples:
- ukraine-donate[.]org
- help-for-ukraine[.]eu
- support4ukraine[.]info
- ukrainesolidarity[.]org
- ukraine-foundation[.]com
- help-ukraine-compaign[.]com
Some of these domains could be used as fronts for financial scams or phishing campaigns targeting people interested in supporting Ukraine. Individuals and entities alike should be cautious with calls for donations sent via email or posted on social media. Some of the malicious domains still host content or redirect to other websites. Here are some examples.
Furthermore, some malicious domains also used the text string “news,” meaning threat actors could potentially take advantage of the global interest in the Russia-Ukraine conflict. It’s best to watch out for domains under the .news top-level domain (TLD) space as well as those posing as hosts for news websites.
While some of the digital properties in this study may have been added by well-intentioned individuals and organizations, others may not be as innocent. Quite a few have already figured in malicious campaigns, and threat actors may continue taking advantage of people’s reactions toward the Russia-Ukraine conflict.
WhoisXML API’s WHOIS and DNS intelligence can uncover and attribute suspicious domains related to NFT and other mechanisms favored by scammers. Contact us for more information.
– Jonathan Zhang is the founder and CEO of WhoisXML API—a domain and IP data intelligence provider that empowers all types of cybersecurity enterprises to build better products and achieve greater network security with the most comprehensive domain, IP, DNS, and cyber threat intelligence feeds. WhoisXML API also offers a variety of APIs, tools, and capabilities, including Threat Intelligence Platform (TIP) and Domain Research Suite (DRS).

Precise and exhaustive data is vital for cyber-security professionals to analyze and prevent cyber crime. Whois XML API offers a comprehensive collection of domain, WHOIS, DNS and threat intelligence data feeds that are essential to their work. It’s an exhaustive Cyber-security package that offers a maximum coverage of both real-time and historic data, complete with instruments for threat hunting, threat defense, cyber forensic analysis, fraud detection, brand protection, data intelligence enrichment across variety of SIEM, Orchestration, Automation and Threat Intelligence Platforms.
The post Russia’s Invasion Of Ukraine: From Digital Spillovers To Phishing Sites appeared first on Cybercrime Magazine.
[ad_2]
Source link