[ad_1]

Historical WHOIS information can uncover investigative breadcrumbs that are otherwise hidden
– Jonathan Zhang, CEO at Whois XML API
Walnut, Calif. – Dec. 19, 2021
We saw a tremendous increase in the volume of phishing attacks in 2020 and 2021, most of which took advantage of the COVID-19 pandemic in more ways than can be counted.
As leaders in the cybersecurity community, we strive to do everything we can to mitigate the threat. We can go defensive by blocking risky and suspicious domains and traffic, responding promptly to incidents, and educating stakeholders about phishing. We also need to take an offensive stance — seek out the threat actors and their attack vectors by tracing their footprints.
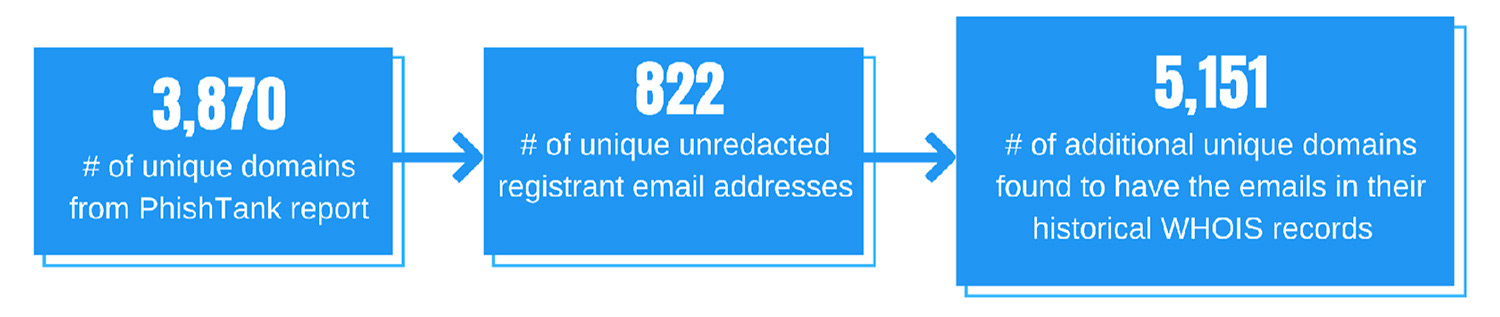
Researchers at WhoisXML API performed a digital footprinting analysis of more than 3,800 verified phishing hosts using historical WHOIS data. The key findings of our downloadable white paper “Digging Up Zombie Domains: What WHOIS History Reveals about 3,800+ Verified Phishing Hosts” include the following:
- Phishing hosts can be both new and old domains, though our data shows that around 51 percent of them were more than a year old when they were reported on PhishTank. A quarter of them were created more than a decade ago.
- Available domains may have a malicious past. About 46 percent of the phishing hosts are available for registration despite having been used by threat actors between March 1 and May 31, 2020.
- The breadcrumbs the phishing domains left found through WHOIS history checks led us to more than 5,000 additional potentially risky or suspicious domains.
- All TLDs, regardless of registry and registrar, are prone to abuse. The phishing hosts in our study mostly fell under .com, .net, .co, .ru, and .org.
Overall, the research highlights the capacity of historical WHOIS data to augment cybersecurity processes, both offensive and defensive.
How WHOIS History Can Help with Attribution Analyses
Based on the white paper, historical WHOIS information can uncover investigative breadcrumbs that are otherwise hidden. This historical ownership data can be traced to the beginning of a malicious domain’s life cycle and lead to significant connections worth scrutinizing.
Of the 3,870 unique phishing hosts PhishTank verified in June 2020, WHOIS history checks uncovered 1,421 unique registrant email addresses used when the domains were first created. More than half of them were unredacted, possibly since they were registered prior to the implementation and global repercussions of the General Data Protection Regulation (GDPR).
In an offensive cybersecurity context, the discovery of these email addresses is significant. It’s one step closer to seemingly elusive threat actors or their attack vectors at the very least.
Using WHOIS History Breadcrumbs to Uncover Suspicious Footprints
The unredacted email addresses exposed by WHOIS history checks led to the discovery of more than 5,000 associated domains — those that contain the registrant email addresses in their historical WHOIS records at some point. These domains are not found in the initial dataset from PhishTank.
Further analysis and investigation can be done on these additional domains as part of cybersecurity defense strategies. They can be fed to security solutions to see if they would be flagged, and their current WHOIS records can be analyzed to find malicious connections.
Phishing has always been a pressing problem in the cybersecurity community, but it has become a household name in the past two years. Even then, threat actors have managed to make their tactics more persuasive and evasive. We have to employ all possible means to stay ahead of them, and WHOIS history checks could provide the breadcrumbs leading to this end.
Don’t hesitate to contact us for possible security research collaborations and learn more about how WHOIS history data can help augment your cybersecurity strategies and solutions.
– Jonathan Zhang is the founder and CEO of WhoisXML API—a domain and IP data intelligence provider that empowers all types of cybersecurity enterprises to build better products and achieve greater network security with the most comprehensive domain, IP, DNS, and cyber threat intelligence feeds. WhoisXML API also offers a variety of APIs, tools, and capabilities, including Threat Intelligence Platform (TIP) and Domain Research Suite (DRS).

Precise and exhaustive data is vital for cyber-security professionals to analyze and prevent cyber crime. Whois XML API offers a comprehensive collection of domain, WHOIS, DNS and threat intelligence data feeds that are essential to their work. It’s an exhaustive Cyber-security package that offers a maximum coverage of both real-time and historic data, complete with instruments for threat hunting, threat defense, cyber forensic analysis, fraud detection, brand protection, data intelligence enrichment across variety of SIEM, Orchestration, Automation and Threat Intelligence Platforms.
The post Digging Up Zombie Domains: 3,800 Phishing Hosts appeared first on Cybercrime Magazine.
[ad_2]
Source link